The Midmarket IT Dilemma: Why Intelligent Autonomous IT Operations Are No Longer Optional
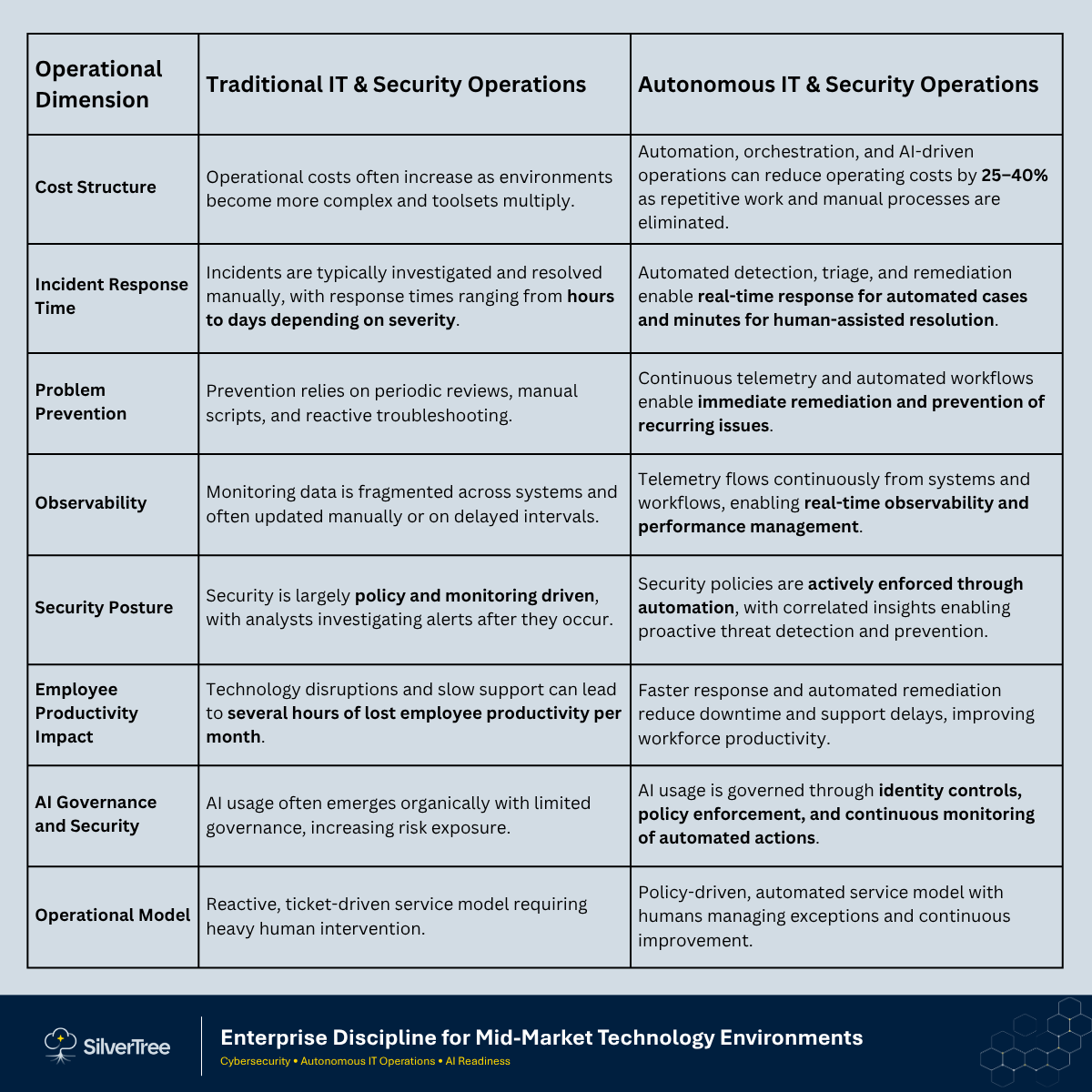
Mid-market IT teams running three to five people are being asked to manage workloads built for fifteen. The ticket queue grows. The security backlog grows. AI tools appear in the environment before anyone has reviewed them. The operating model stays the same. This article makes the case that reactive, ticket-based IT operations cannot scale to meet what AI adoption is adding to the environment, and that autonomous operations, where policy enforcement, incident response, and AI governance run at machine speed, is the only model that closes that gap without proportional headcount increases

The Midmarket IT Dilemma: Why Intelligent Autonomous IT Operations Are No Longer Optional
Midmarket enterprises are at a crossroads. Pressured by rising complexity, workforce demands, compliance obligations, and constrained resources, traditional approaches to IT service delivery are no longer sustainable. The promise of digital transformation remains distant when core IT operations are stuck in reactive cycles and fragmented toolsets.
The Structural Tension Facing the Midmarket
Organizations in the $50 million to $1 billion revenue range operate in a uniquely challenging environment. They are expected to meet enterprise-level demands for performance, security, resilience, and innovation, yet they must do so without the staffing scale or capital depth available to larger enterprises. The result is structural tension. Enterprise expectations collide with midmarket budgets. Hybrid cloud environments, SaaS applications, remote endpoints, and legacy systems must be managed cohesively, often by lean IT and security teams. Tool sprawl proliferates without integration, creating fragmented data, siloed workflows, and a lack of end-to-end visibility. AI adds another layer of sprawl, often invisible, because usage is distributed across browser tools, copilots, embedded SaaS assistants, plugins, and API-driven agents that can access corporate data and take action across systems. At the same time, most service operations remain reactive and ticket-centric, relying on legacy help desk models that are manual, slow, and increasingly unable to scale.
The consequences are predictable and costly. High Mean Time to Resolution reduces productivity and increases business risk. Missed SLAs and a deteriorating digital employee experience undermine workforce effectiveness. Shadow IT and audit failures emerge in the absence of strong governance and integrated access control. Overstretched teams spend most of their time keeping the lights on, leaving little bandwidth for strategic initiatives or continuous improvement. These outcomes are not the result of poor leadership; they are the inevitable result of an outdated operating model attempting to meet modern business demands.
Enter Intelligent Autonomous IT Operations
We are now entering the era of Autonomous IT Operations, a transformative model that shifts IT from reactive firefighting to intelligent, self-directed service delivery. For midmarket organizations, this model provides a path to enterprise-grade service quality, and security risk reduction without enterprise-level cost or complexity.
Faster resolution, fewer repetitive tickets, predictable policy-based service delivery, real-time correlation of incidents enabling increased security, and freed IT bandwidth for innovation become attainable outcomes rather than aspirational goals.
Autonomous IT is also becoming the only viable way to manage AI risk at scale. As organizations adopt copilots, automated workflows, and agentic tools, the rate of change in access permissions, data movement, and system interactions increases dramatically. Without autonomous governance, enforcement, and response, AI adoption can outpace an organization’s ability to control it—creating a material operational and security exposure. Autonomous IT provides the policy-driven automation and real-time telemetry required to keep AI secure, compliant, and reliable in production.
The New Risk Layer
AI Expands the Attack Surface Faster Than Humans Can Defend. AI is accelerating business productivity, but it is also accelerating operational risk. The midmarket is now contending with a new class of “machine-speed” exposure that traditional ticket-based IT and security operations cannot keep up with. AI introduces new paths for data leakage (prompts, uploads, and training behavior), new identity risks (agent credentials, API tokens, delegated access, and over-privileged connectors), and new “autonomous execution” risks where systems can take actions at scale with minimal human oversight. This is not theoretical. In many organizations, AI adoption has already outpaced governance, creating a shadow layer of tools, plugins, and data flows that bypass standard change control and security review.
This is why Autonomous IT Operations are no longer optional. When workflows and agents can act in seconds, defensive controls and operational response must also operate in seconds. The future state is not “AI plus humans watching dashboards.” It is policy-based, continuously monitored, automated enforcement that prevents risky actions before they happen and contains incidents immediately when they do. Autonomous IT becomes the control plane that makes AI safe to use at enterprise speed: identity guardrails, data guardrails, approved tooling guardrails, and automated remediation when guardrails are breached.
In practical terms, leaders should treat AI like a new production environment: it needs an operating model with clear approvals, least-privilege access, telemetry, change control, and tested response procedures. Without these, AI increases the likelihood of confidentiality breaches, compliance failures, service disruptions, and fraud. With them, AI becomes a reliable business enabler rather than a fast-moving risk multiplier.
The Five Foundational Capabilities Enabling the Shift
Autonomous IT is made possible by the convergence of five foundational capabilities.
1. Enterprise Data Fabric: Eliminating Operational Silos
The first is an enterprise data fabric, which eliminates the silos that have historically fragmented IT environments. Traditional architectures hold pieces of the story in disconnected systems, but an enterprise data fabric aggregates telemetry, asset metadata, service history, user context, and policy into a unified intelligent layer. This unified layer functions as a nervous system, enabling real-time awareness, insight, and decision-making across the environment.
2. Workflow Automation and Service Orchestration: Enforcing Discipline at Scale
The second capability is workflow automation and service orchestration. Modern low-code automation platforms allow organizations to design and deploy complex, cross-domain workflows that enforce consistency, reduce human error, and drive policy-compliant outcomes. Whether provisioning a user, remediating a vulnerability, or managing a cloud resource, these orchestrated workflows shift IT operations from manual intervention to structured execution, freeing personnel to focus on higher-value initiatives.
3. AI and Machine Learning: Shifting Humans to Exception Handling
The third capability is AI and machine learning–driven decision support. Advances in machine learning, natural language processing, and agentic AI have expanded what is operationally possible. AI can autonomously triage incidents, classify service requests, correlate events across domains, and resolve common issues without human intervention. In this model, human operators become exception handlers and risk owners rather than first responders, setting policy, approving changes, and managing the rare edge cases, while autonomous controls execute the routine enforcement and remediation that must occur at machine speed while allowing teams to scale more effectively and focus their time on enabling continuous improvement and enabling better business performance.
4. Unified Observability: From Monitoring to Self-Healing
The fourth capability is unified observability and experience monitoring. Autonomous operations require holistic visibility into infrastructure health, application performance, security posture, and digital employee experience. Modern observability platforms provide correlated insights that enable self-healing systems capable of detecting, diagnosing, and correcting issues before users are even aware, thereby strengthening reliability and trust in IT services. The ability to see what is happening comprehensively is key to driving more responsive service and proactive performance improvement.
5. Identity and Policy Guardrails: Governing Autonomous Action
Autonomy without guardrails is simply unmanaged automation. The fifth capability is identity and policy guardrails that determine what AI systems and workflows are allowed to access, what actions they can take, and under what conditions. This includes least-privilege access for agents and connectors, strong authentication, continuous authorization, policy-based data handling, and automated enforcement of approved tools and approved data sources. These guardrails ensure that AI-enabled workflows remain compliant, auditable, and reversible—especially critical when the “operator” is an automated agent rather than a human.
Why This Moment Is Different
These capabilities have converged at a pivotal moment. Cloud-native platforms are modular, scalable, and designed to be automated. Open telemetry and API accessibility have broken down the walls between systems, allowing organizations to extract high-fidelity, real-time data across applications, endpoints, networks, and infrastructure. Breakthroughs in machine learning and natural language interaction enable intelligent agents to interpret user intent and take action in real time. At the same time, low-code and no-code platforms have democratized automation, allowing organizations to scale intelligent workflows quickly and affordably. Rising pressure around cybersecurity, compliance, and distributed workforces further accelerates the need for a proactive, adaptive, and secure-by-design operating model.
AI has also changed the time constants of risk. A misconfiguration, over-privileged connector, or unsafe data sharing pattern can propagate instantly across users and systems. The organizations that succeed will be those that can detect, decide, and act in near real time through automated controls and orchestrated response—making autonomy a security requirement, not just an efficiency upgrade.
An Evolutionary Path, Not a Disruption Event
Transitioning to Autonomous IT does not require wholesale replacement of existing investments. It is a deliberate and evolutionary journey that transforms one process, one workflow, and one insight at a time. Success begins with unifying the data ecosystem to eliminate silos and establish a trusted operational fabric. It continues by automating repeatable, cross-domain workflows that reduce manual toil while enforcing consistency and compliance. It matures by embedding AI at decision points such as incident triage, ticket classification, and predictive scaling. It stabilizes through full-stack observability that transforms monitoring into intelligent auto-remediation. Ultimately, it requires redefining IT roles from reactive issue resolution to proactive experience engineering and automation design.
The Imperative for Midmarket Leaders
For midmarket organizations, the demand for secure, agile, and cost-effective IT operations has never been greater. Attempting to meet these demands with static workflows and reactive models only widens the gap between expectations and capability. Autonomous IT represents a paradigm shift that enables proactive, intelligent, and self-healing operations while freeing IT teams to focus on innovation and broader business transformation.
This shift is not about replicating enterprise complexity; it is about leveraging advancements in data fabrics, orchestration, AI, and observability to reinvent how IT is delivered and consumed in the midmarket. The convergence of capability and necessity makes Autonomous IT both feasible and imperative. For leaders navigating rising expectations with constrained resources, the time to act is now.
As midmarket leaders consider how and who provide their IT services, they should pick a platform and partner that is focused on meeting them where they are and enabling them to take full advantage of the capabilities associated with Autonomous IT capabilities. AI is the future transaction layer, and data is the digital fuel of business. Autonomous IT brings together these and the observability to enable continuous performance improvement. This allows their resources to be freed up to provided higher value services that enable better productivity and business responsiveness. The IT platform is not only about managing the legacy technology it must be able to enable the transition to the new model of Intelligent Service Provision across all layers to the process and technology stack including the emerging capabilities such as Agentic AI.
The emerging reality is that AI governance cannot remain a policy document and annual training exercise. It must be operationalized. Boards, regulators, customers, and insurers will increasingly expect proof that AI use is controlled: approved tools, controlled data pathways, least-privilege access, audit trails, and incident response readiness. Autonomous IT is the mechanism that turns those expectations into enforceable, measurable outcomes, making it a prerequisite for safe AI adoption, not an optional modernization project.
A Recommended Approach for Getting Started
For midmarket leaders ready to act, the path forward does not begin with a massive transformation program. It begins with clarity. Before committing to platforms or partners, establish an honest baseline: where are the highest-risk gaps in your current operating model, where is AI already in use governed or not, and what workflows are consuming the most manual effort with the least reliability? That assessment is the essential first step. It surfaces the use cases most likely to deliver near-term value, identifies the data and security constraints that must be addressed before automation can scale safely, and produces a phased roadmap that business and technology leaders can align on and fund with confidence. From there, the journey follows a logical sequence: stabilize the operational foundation, automate the highest-friction workflows, embed AI at the decision points where speed and accuracy matter most, and build the observability and governance layer that keeps autonomous operations compliant and auditable as they scale. The right partner is one that operates at the intersection of IT operations, security, data, and AI, willing to begin with an assessment, demonstrate value before asking for a long-term commitment, and bring both strategic clarity and operational depth to deliver measurable outcomes. The time to begin is now. AI is not a future consideration. It is already present in your environment, used by your employees, embedded in your SaaS tools, and interacting with your data. The only question is whether it is operating under a governance model capable of managing it safely.